Significance
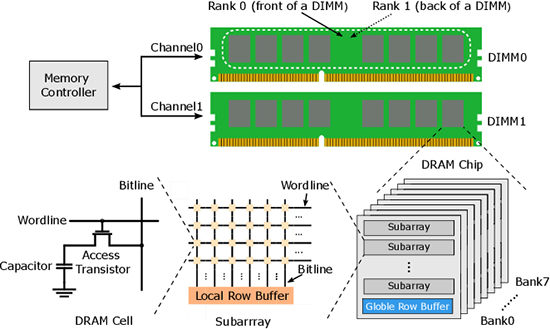
For cybersecurity, vulnerabilities continue to evolve, and one such vulnerability that has gained significant attention is Rowhammer. Rowhammer is a hardware reliability concern that arises when an attacker repeatedly accesses specific DRAM (Dynamic Random-Access Memory) rows to cause unauthorized changes in physically adjacent memory rows. This vulnerability become a critical concern in the field of computer security due to its potential to enable various attacks, including privilege escalation, sandbox escapes, and breaking cloud isolation. The severity of the Rowhammer problem lies in its exploitation of fundamental DRAM circuit behavior, where bit flips occur when a specific DRAM row is repeatedly activated and precharged, resulting in electromagnetic interference between the aggressor row and its neighboring rows, causing cell capacitors in victim rows to leak faster than normal operation and eventually leading to bit flips. Rowhammer is not confined to specific DRAM generations; it affects both DDR3 and DDR4 DRAM memories making it a widespread and persistent concern across various hardware platforms. Over the years, numerous Rowhammer mitigation techniques have been proposed, both at the hardware and software levels. However, existing mitigation schemes have proven to be either ineffective against emerging Rowhammer attacks or have incurred substantial implementation overhead.
The research study recently published in the peer-reviewed Journal IEEE Transactions on Computer-Aided Design of Integrated Circuits and Systems, led by Dr. Tyler K. Bletsch from Duke University, Dr. Biresh Kumar Joardar, and Professor Krishnendu Chakrabarty from Arizona State University, marks a significant advancement in the ongoing battle against Rowhammer. The authors developed a machine learning (ML)-based technique designed to provide fast and efficient detection of various Rowhammer attacks while maintaining low hardware overhead. They proposed a solution which leverages machine learning models to analyze memory access patterns and distinguish between benign memory accesses and malicious Rowhammer attacks. By using this ML approach, the authors have successfully developed a Rowhammer mitigation solution that offers several notable advantages. First, the ML model can accurately detect various Rowhammer attacks, including the recently proposed TRRespass, Half-double, and Blacksmith attacks, which have posed challenges to existing mitigation techniques. Secondly, the proposed solution is implemented entirely on-chip, which means it does not require significant external hardware resources, making it a practical and cost-effective choice for mitigating Rowhammer attacks. Moreover, the experimental analysis demonstrated that the ML method introduces significantly lower power and area overhead compared to existing mitigation techniques like Graphene and Blockhammer, with 5% and 19% lower power overhead, respectively.
The researchers’ experimental evaluation of the ML-based Rowhammer mitigation technique provided compelling evidence of its effectiveness. The researchers conducted their experiments using the Gem5 simulator, which emulates a four-core system with various DRAM configurations. They employed a diverse set of applications, including benign applications and Rowhammer attacks, to evaluate the proposed solution’s performance and accuracy. The experiments revealed that Rowhammer attacks were successful on commercial DDR4 DRAMs, even with Targeted Row Refresh (TRR) enabled. This highlights the urgent need for more effective mitigation techniques.
A critical aspect of the study was the creation of a diverse dataset that included both benign memory access patterns and Rowhammer attacks. Memory-access traces were collected using cycle-accurate simulations on the Gem5 platform. The ML model demonstrated high accuracy in detecting Rowhammer attacks while introducing minimal performance overhead. It outperformed existing techniques in terms of area and power overhead, making it a practical choice for implementation. Moreover, the ML solution exhibited robust performance even when HCfirst (the number of hammers required to cause a bit flip) was as low as 10K. This suggests that the model can adapt to future reductions in HCfirst, which is expected as DRAM technology advances.
The authors’ findings represent a significant step forward in addressing the persistent threat posed by Rowhammer attacks. By harnessing the power of machine learning, the researchers have developed a practical and efficient mitigation technique that not only detects various Rowhammer attacks but also minimizes power and area overhead. The scalability of this solution ensures its relevance in future hardware development.
Reference
Biresh Kumar Joardar; Tyler K. Bletsch; Krishnendu Chakrabarty. Machine Learning-Based Rowhammer Mitigation IEEE Transactions on Computer-Aided Design of Integrated Circuits and Systems ( Volume: 42, Issue: 5, 2023)
Go to IEEE Transactions on Computer-Aided Design of Integrated Circuits and Systems
 Advances in Engineering Advances in Engineering features breaking research judged by Advances in Engineering advisory team to be of key importance in the Engineering field. Papers are selected from over 10,000 published each week from most peer reviewed journals.
Advances in Engineering Advances in Engineering features breaking research judged by Advances in Engineering advisory team to be of key importance in the Engineering field. Papers are selected from over 10,000 published each week from most peer reviewed journals.